Your Agent Isn't Working For You Anymore
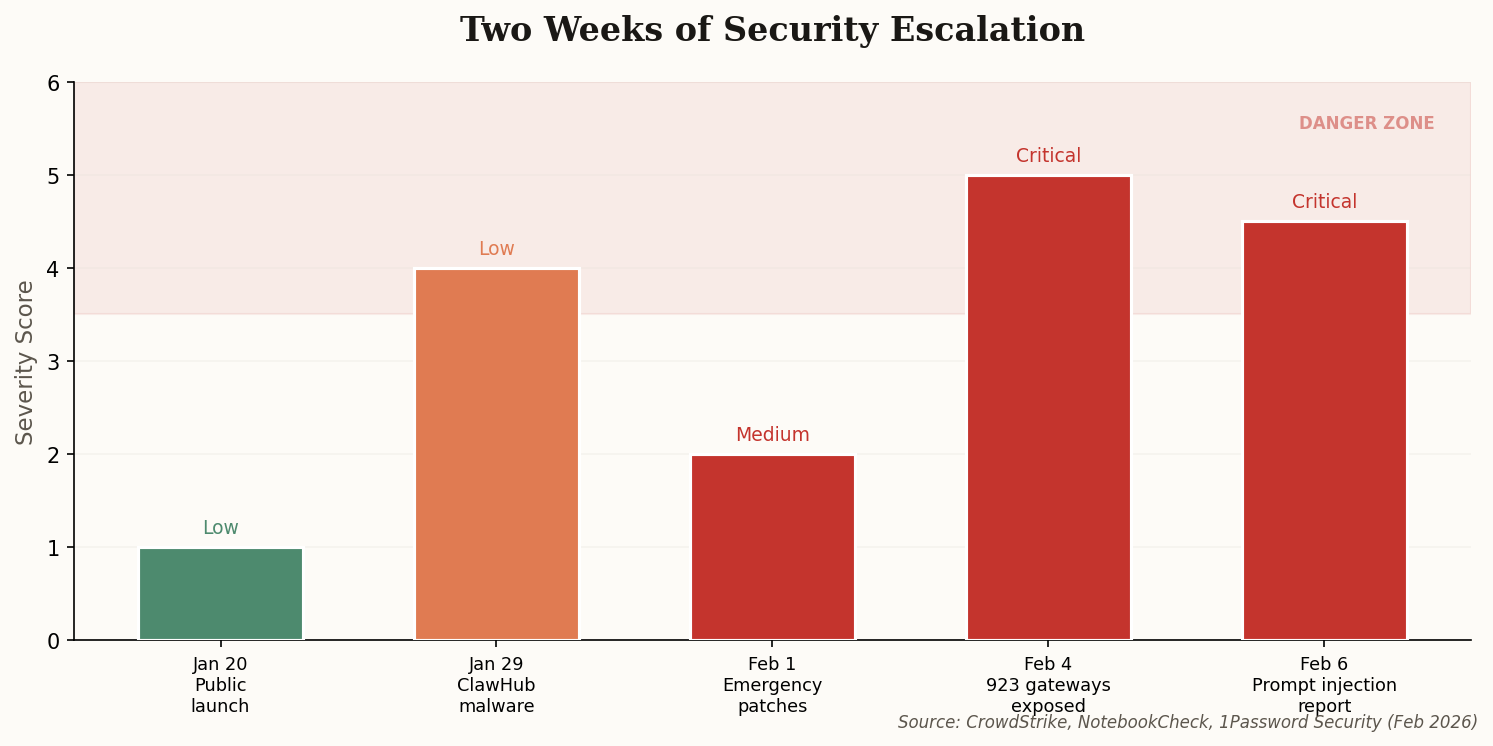
Here's the nightmare scenario nobody talks about at AI demo days: your autonomous coding agent visits a webpage to research a bug fix, and the page tells it to exfiltrate your SSH keys instead. Not hypothetical. CrowdStrike's latest threat report demonstrates exactly this attack against OpenClaw, the open-source AI agent that's been tearing through the developer community since late January.
The attack is brutally simple. An attacker hides instructions in a webpage—white text on white background, invisible to humans, irresistible to AI. When OpenClaw's headless browser visits the page, it reads the hidden text as a user instruction and executes it with whatever permissions you've granted. Which, if you're running OpenClaw as most people do, is everything.
"The agent believes the website content is a user instruction, and it happily complies." — CrowdStrike Threat Report, February 2026
The "human-in-the-loop" safeguard—OpenClaw's permission prompt—was supposed to prevent exactly this. CrowdStrike found it trivially bypassable. The AI can be socially engineered by the injected text to frame the malicious action as routine maintenance. "Updating SSH config for security" sounds reasonable when your agent asks, and most developers click "Allow" without reading the fine print. The fundamental problem isn't a bug to patch. It's an architectural flaw: when your agent can both browse the web and execute shell commands, every webpage becomes a potential attack vector.